1. Build under NDA in secured local AI environment
We design and validate workflows inside controlled boundaries with explicit access paths, auditability, and technical evidence.
Our model is structured to protect client confidence while accelerating delivery: build under NDA in a secured local AI environment, migrate into client-controlled infrastructure, then support reliable operations.
We design and validate workflows inside controlled boundaries with explicit access paths, auditability, and technical evidence.
We transfer deployment assets, configuration patterns, and operating controls so architecture remains repeatable and owned by the client.
We establish monitoring, runbooks, and change controls so systems stay reliable, supportable, and aligned with regulated obligations.
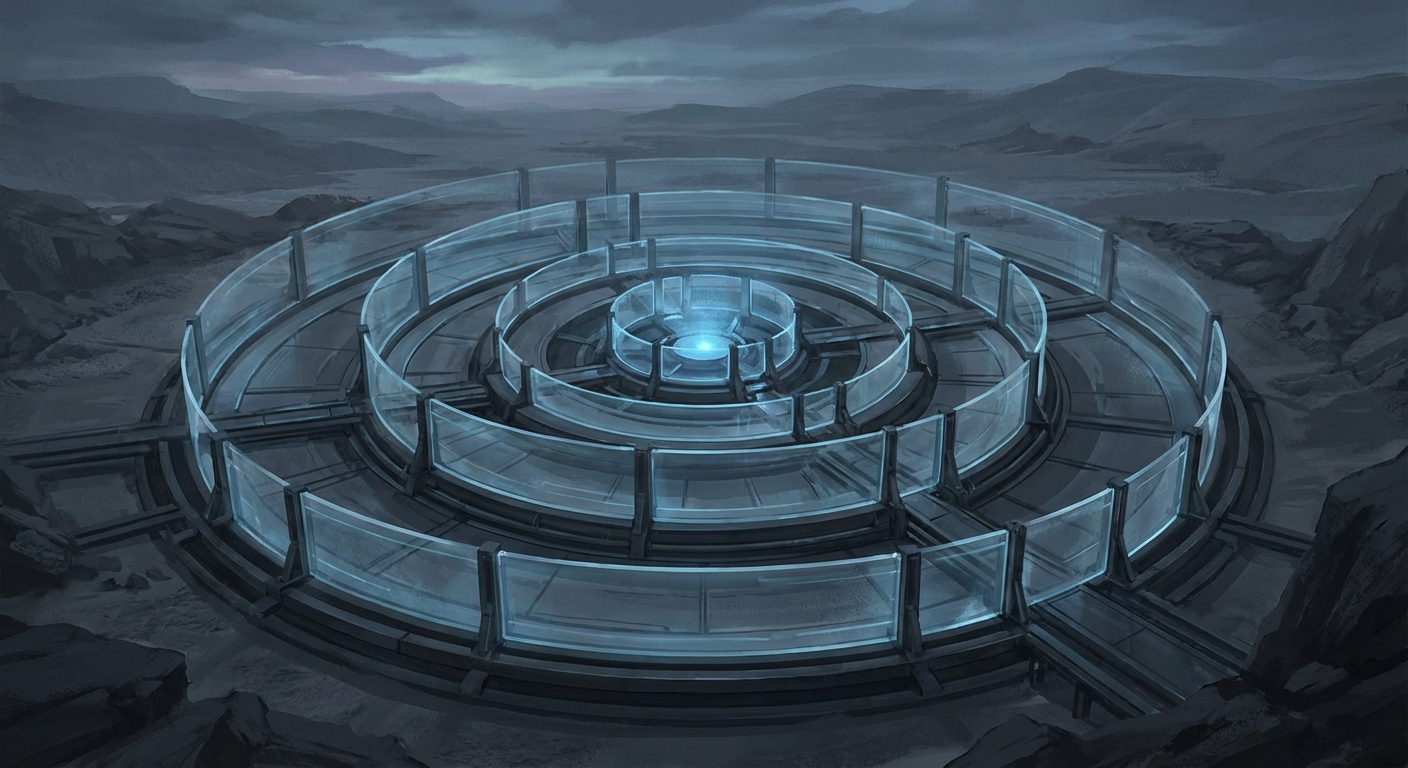
We treat containment boundaries as a first-class design element from architecture through runtime operations.
For practical examples, review our case studies.